U.S. Authorities Dismantle Russian Ransomware Infrastructure, Seize $1 Million in Bitcoin
In a major international cybercrime operation, the U.S. Department of Justice has announced the takedown [...]
Aug
Hackers Bypass Microsoft Defender to Deploy Ransomware, Report Finds
A recent cybersecurity report reveals that Microsoft Defender, Windows’ built-in security tool, is facing a [...]
Aug
Newly Discovered TETRA Encryption Flaws Put Critical Communications at Risk
A new wave of security vulnerabilities has been uncovered in the Terrestrial Trunked Radio (TETRA) [...]
Aug
Columbia University Cyberattack Exposes Personal Data of Over 860,000 Individuals
Columbia University recently experienced a significant cyberattack that compromised the personal information of more than [...]
Aug
Malicious RubyGems and PyPI Packages Target Credentials and Cryptocurrency, Forcing Security Measures
A new wave of malicious software packages has been uncovered impacting two major software ecosystems: [...]
Aug
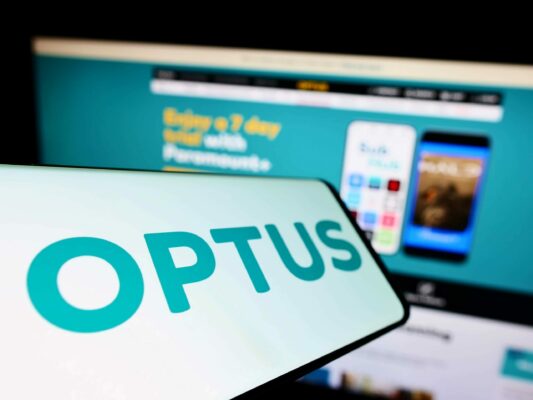
Australian Regulator Takes Legal Action Against Optus Following 2022 Data Breach Affecting Millions
The Australian Information Commissioner (AIC) has initiated civil proceedings against telecommunications provider Optus due to [...]
Aug
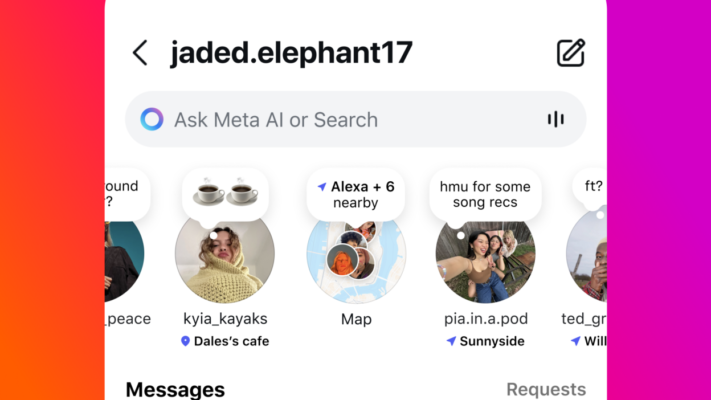
Instagram’s New Map Feature Triggers Privacy Concerns Over Location Sharing
Instagram’s recently introduced Map feature is drawing attention — and not for the reasons the [...]
Aug
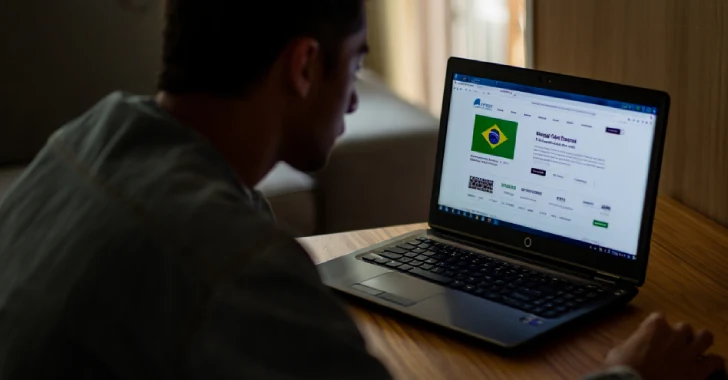
AI Tools Power Brazilian Phishing Scheme as Efimer Trojan Targets 5,000 Crypto Users
Cybersecurity experts have uncovered a sophisticated phishing campaign in Brazil that exploits legitimate generative AI [...]
Aug
Organizations Urged to Patch Critical Microsoft Exchange Hybrid Vulnerability
Organizations operating hybrid Microsoft Exchange deployments have been alerted to a critical security vulnerability that [...]
Aug
Google Confirms It Was Targeted in Salesforce Data Breach Campaign
Google has acknowledged that it was among the companies affected by a broader data theft [...]
Aug

 Español
Español